See Yourself in Cyber: Update Your Software
October 27, 2022 | Authored by Dopkins Assurance Services Group
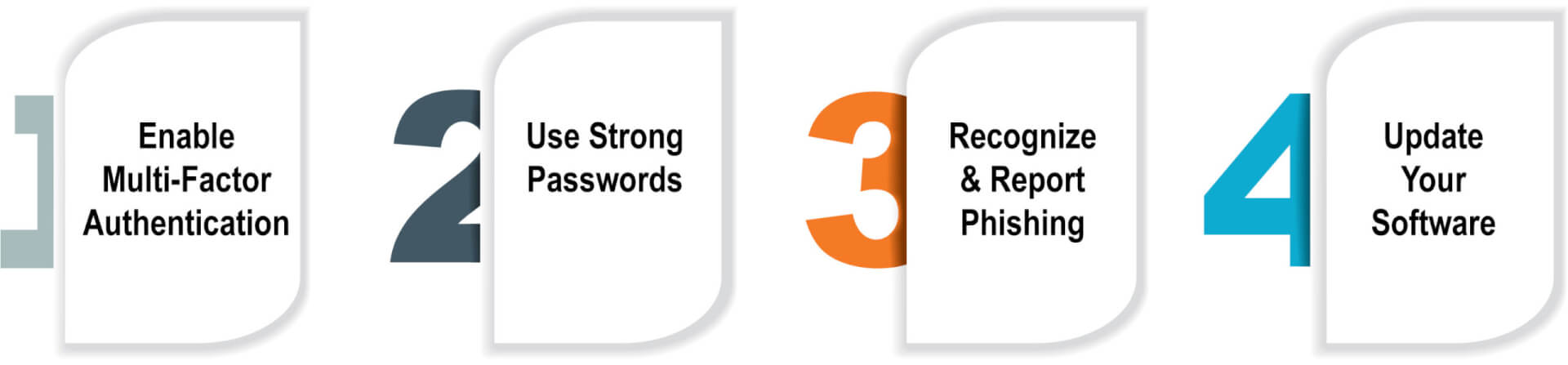
For the past 19 years, October has been recognized as Cybersecurity Awareness Month in the United States. This year the Cybersecurity and Infrastructure Security Agency (CISA) and the National Cybersecurity Alliance (NCA) have collaborated to create a campaign designed to provide information and resources to help educate the public. Their campaign theme, “See Yourself in Cyber,” reinforces the human element of Cybersecurity. With this campaign they have established four things you can do to increase your Cybersecurity posture. To support this campaign Dopkins & Company has released a weekly blog discussing each of these topics:
- Enable Multi-Factor Authentication
- Use Strong Passwords
- Recognize and Report Phishing
- Update Your Software
While reading these blogs keep the theme (See Yourself in Cyber) in mind. Each of these key action steps is something YOU can do to increase Cybersecurity at home, work, and school. While each blog will discuss the actions individuals should take, they will also touch on how businesses can help their employees succeed with each action.
You can view the campaign directly on CISA’s website at https://www.cisa.gov/cybersecurity-awareness-month.
Update your Software
This month’s final action item is to update your software. Before you can update your software, you will need to know what software you are using. This requires an accurate and up-to-date list of all software in your environment and should include the version you are using and the most current version available.
One of the first considerations is the age of your software and whether it is in support and still receiving updates from the vendor. A good example is Windows 7, Microsoft ended support for the an operating system on January 14, 2020 meaning they have not released routine updates in nearly three years. The same situation will happen for Windows 10 on October 14, 2025 giving everybody three years from now to update to Windows 11 or a future version of Windows. It is possible that you still have legacy software running in your environment that has been around for 5, 10, or even 20+ years. If this software has not been kept current by the vendor there will be significant vulnerabilities that can be compromised. If your vendor is no longer providing updates you will need to evaluate the risk of keeping the legacy software vs changing to a newer product.
Types of updates
After you confirm your software is receiving updates you will have to know what is included in the updates you receive. Most vendors will release occasional version (feature) updates. These updates are meant to increase the usefulness or functionality of a product. They may include changing how the software looks, where menu items are, or completely new things to do. It is not urgent to install version updates unless they also include changes to fix bugs and vulnerabilities. But, these types of changes are usually released in the more frequent security updates (known as patches). Some vendors release security updates on a schedule while others release them as needed. Patches do not change the overall software but just small pieces of the code. Patches are meant to fix known vulnerabilities that can be used against you. These patches should be installed as soon as they can be. Often times the vulnerabilities are actively being exploited on other systems. If the vulnerabilities were previously unknown, the release of the patch allows them to be discovered and makes the unpatched system more of a target than before the release of the patch.
Microsoft releases security updates for supported Windows Operating Systems in the afternoon of the second Tuesday of each month, in what is known as Patch Tuesday. This past month was on the 11th, in November it will be on the 8th. Because of this, the following day is known as Exploit Wednesday, where attackers will begin to exploit the newly disclosed vulnerabilities.
A final update to consider is definition updates. Within some software, primarily anti-virus, there are definitions. These update independently from the software itself and should always be kept current. Some definitions update constantly and usually software can be set to check automatically on an interval (i.e., every hour).
Cloud Software
There has been a significant move to cloud software the past several years. Cloud software is any software hosted by someone other than your own organization. This includes websites you sign into including payroll, HR, asset management, etc. You may also sign into an entirely different system in order to access software. Regardless of how it is accessed you still need to verify your software is properly updated. Many times, when you contract with a third-party, they will manage the updates for you and keep everything up-to-date, but this needs to be confirmed.
Barriers to Implementing
This blog led with the recommendation of creating a software inventory to assist tracking updates. While this is important to ensure no software is overlooked, it should not take priority over the updates themselves. Both tasks can be done simultaneously with the inventory serving as the initial documentation of the status of updates. A more thorough inventory can be developed after it is ensured software is current.
One of the largest concerns with running updates or patches is the downtime caused while they are installed and the system reboots. This will cause each employee to lose time while their workstation updates. Additionally, servers will need to be rebooted which can cause additional down time for everybody. Scheduling servers (and possibly even workstations) to update off-hours during a maintenance window will minimize the impact. This should always be done with operations in mind, but should not be avoided altogether. Having an effective patch management platform will be greatly beneficial in tracking and coordinating the logistics of updating all systems. This will help automate the process as well as scheduling during the appropriate times.
Another large concern is that the update will cause the system, or a component of the system, to stop working properly. This stresses the importance of having backups that can be reverted to if needed. It also makes a case for having a test environment that closely replicates the operating environment.
While addressing the software in your organization don’t overlook any non-business devices used by employees. If employees are allowed to use their own PC to access your system, do they keep it up to date? Same question for personal phones that link to organization email. Your organization’s policies and acceptable use agreements need to address whether employees can use their own devices and the expectations/requirements around such use.
Check out our Cybersecurity Awareness Month 2022 page for more resources.
About the Author
Dopkins Assurance Services Group
Dopkins offers a full range of assurance services that can help improve your financial accuracy. From financial report preparation and audits of historical financial statements to preparation of an array of special attestation reports—we can help translate numbers into accurate management information so you can make knowledgeable decisions. For more information, contact Bart McGloin, CPA, CFE, CFF at bmcgloin@dopkins.com.

