STARTegy: A Strategy for Getting Started with Information Security
A unique combination of your knowledge of your business, and our knowledge of information security controls and how they work together.
Information Security vs Cybersecurity
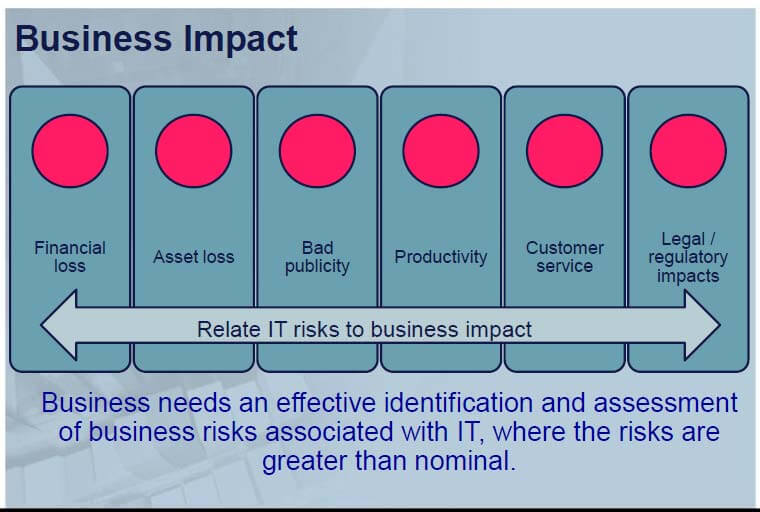
Information is an asset that is essential to an organization’s success, and must be protected from threats, both external and internal.
Information security is needed to ensure business continuity, minimize business risk, and maximize return on investments and business opportunities. An extension of Information Security is Cybersecurity.
Cybersecurity deals with the unique aspect of having systems and data interconnected globally through the internet. (Check out our page on Information Security and download our whitepaper to learn more.)
>> Information security is not just an IT function. Risk is managed through administrative, physical, and technical controls.
STARTegy combines a Risk Assessment, Monthly Focus Sessions, and Employee Training and Testing into one comprehensive two-year program to provide virtual Information Security Officer (vISO) functions.
We’ve provided a summary of each component:
Risk Assessment
|
|
Monthly Focus Sessions
|
|
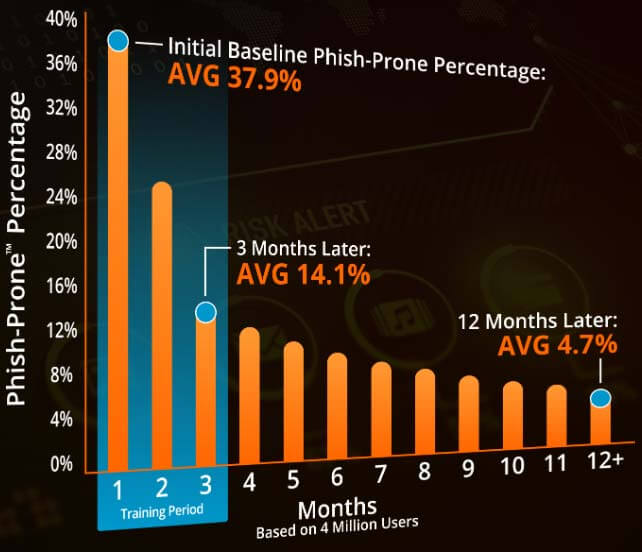
Employee Training and Testing
|
Powered by:
|
vISO (virtual Information Security Officer)
|
|
Got 3 minutes? Watch an introduction to STARTegy:
Register to receive a link to our pre-recorded STARTegy webinar:
More about STARTegy:
- A unique learning and planning process.
- Based on CIS top 20 Critical Security Controls.
- Delivers a starting point for addressing information security risks.